What we do
Transformation
Sustain performance, build lasting organisational change and implement your vision for the future.
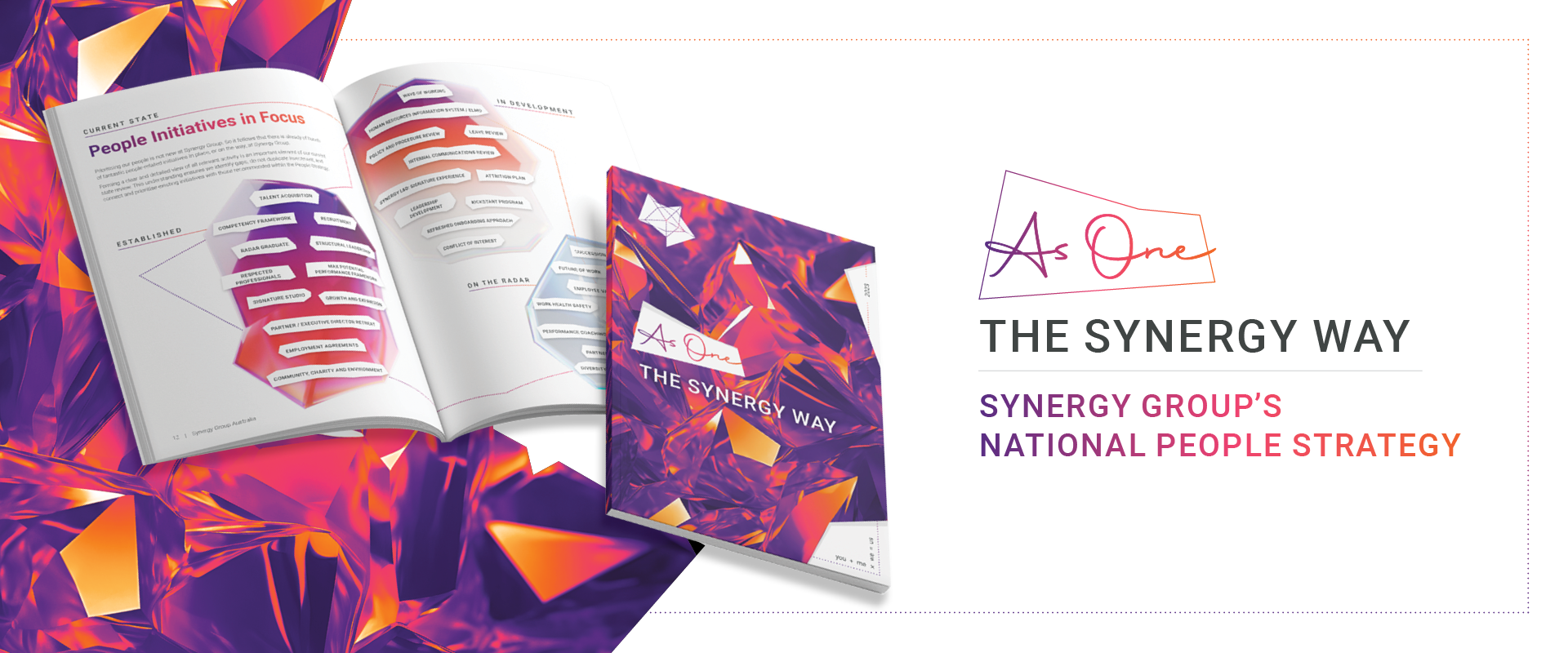
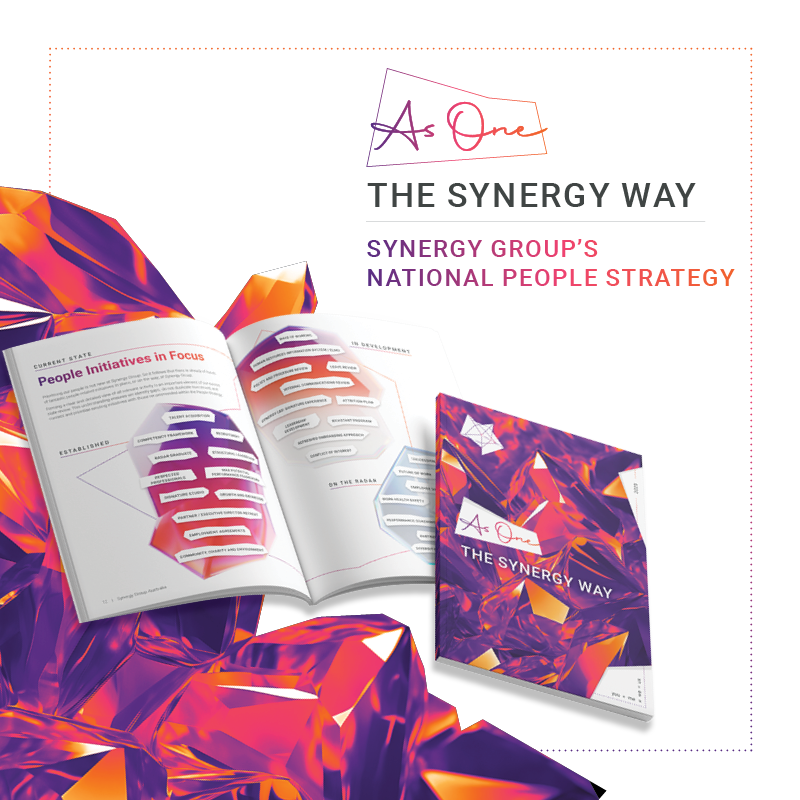
Read MorecreativeXpeople
Design and realise behavioural change, modernise people strategies, communicate with impact and influence.
Read MoreTechnology, Cyber and Data
Digitally enabled solutions, maximising the opportunity of technology.
Read MoreGovernance, Performance and Assurance
Find confidence. Have certainty of performance and action. Find what works, and not.
Read MoreSynergy Law
Supporting Government to become 'future ready', partnering with clients to achieve legally defensible outcomes.
Read MoreHow we think
Passionate about knowledge. Thought leaders with a collective finger on the pulse. We pride ourselves on collaborating with clients to understand the true potential. Get to know us better.